Microsoft has issued an alert about a “massive email campaign” that uses the Java-based STRRAT malware to steal sensitive data from compromised systems while masquerading as a ransomware infection.
The Microsoft Security Intelligence (MSI) team has detailed the specifics of a “massive email campaign” that delivered the StrRAT malware that they discovered last week and published in a series of tweets this week.
StrRAT is a Java-based remote access tool that steals browser credentials, records keystrokes, and takes remote control of infected computers, according to MSI researchers who detailed the malware’s actions in GitHub documentation.
According to them, the RAT also has a module that uses a command-and-control (C2) server command to download an additional payload onto the infected machine.
Also read: Fake Microsoft Authenticator extension spotted in the Chrome Web Store
The RAT is notorious for its ransomware-like activity of appending the file name extension .crimson to files without ever encrypting them, according to the Microsoft Security Intelligence team.
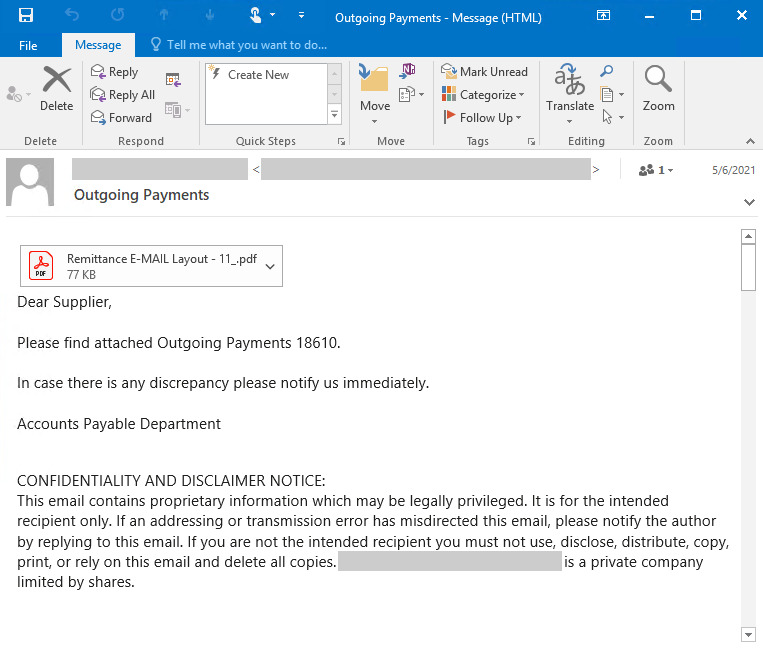
The new wave of attacks, which the company discovered last week, starts with spam emails with the subject line “Outgoing Payments” that trick recipients into opening malicious PDF documents that appear to be remittances but actually bind to a rogue domain and download the STRRAT malware.
The malware includes several features that allow it to collect browser passwords, log keystrokes, and run remote commands and PowerShell scripts, in addition to establishing connections to a command-and-control server during execution.
The Windows malware (version 1.2) was first discovered in phishing emails containing malicious Jar (or Java Archive) attachments in June 2020, according to German cybersecurity firm G Data.
You might also like: Beware: Ficker-info stealing malware is pretending to be Microsoft Store
The RAT focuses on stealing credentials from browsers and email clients, as well as passwords, according to G Data malware researcher Karsten Hahn.
Firefox, Internet Explorer, Chrome, Foxmail, Outlook, and Thunderbird are among the browsers and email clients it supports.
Its ransomware capabilities, on the other hand, are restricted, as the “encryption” stage only renames files with the “.crimson” extension. The files can be accessed normally once the extension has been disabled.
Version 1.5 is also more obfuscated and modular than previous versions, implying that the attackers behind the operation are actively working to improve their toolkit.
Latest: E-commerce giant Mercari data breach: several data exposed